At Cyber Centaurs, we specialize in digital forensics and data breach investigations. Our expertise extends to corporate espionage, trade secret theft, white-collar crime investigations, and commercial litigation matters.
Insights & Investigations
Technical analysis, breach research, and investigative insights for security leaders and legal teams.
DATA BREACH RESOURCES

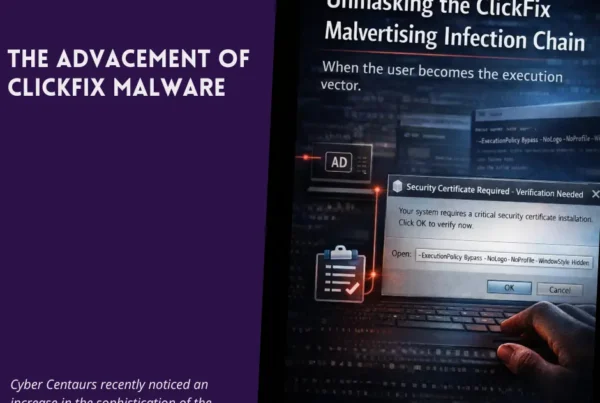
This is Part 3 of a three-part series analyzing a sophisticated ClickFix malvertising campaign. In this series, we cover the initial social engineering (Part 1), the malware’s evasion tactics (Part…

This is Part 2 of a three-part series analyzing a sophisticated ClickFix malvertising campaign. In this series, we cover the initial social engineering (Part 1), the malware’s evasion tactics (Part…
DIGITAL FORENSICS RESOURCES

Across the field of digital forensics, one myth persists with remarkable tenacity: the belief that deleted data is never really gone. This notion, popularized by crime dramas and media portrayals,…
PENETRATION TESTING

Understanding RATs In the dynamic landscape of cybersecurity, the Remote Access Trojan (RAT) emerges as an enduring and sophisticated menace. Functioning as a specialized form of malware, RATs excel in…